Under Vehicle CCTV Inspection
Design of Technology for Verification & Control of Vehicle Access.
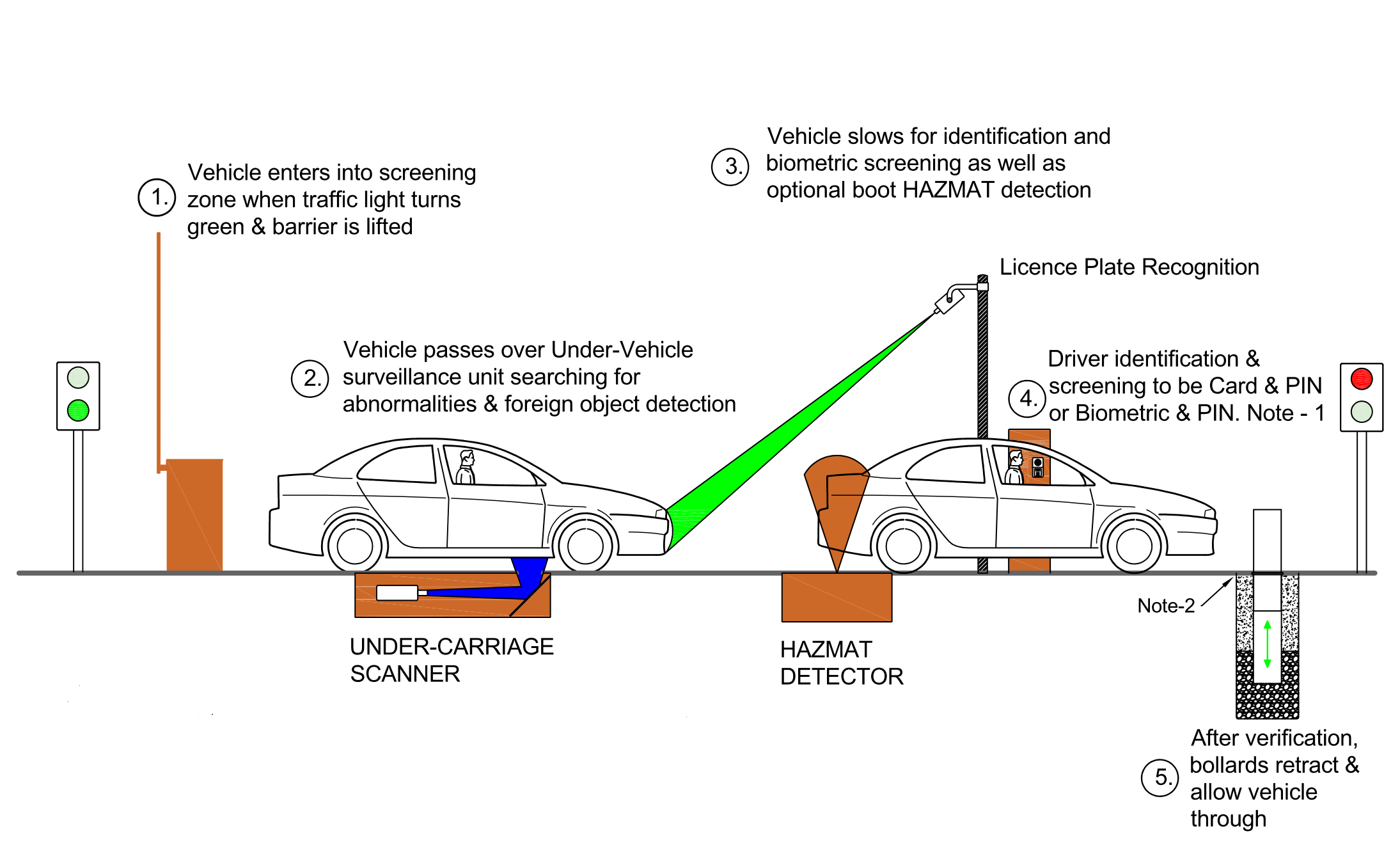
Access Control for Vehicles
Some of the most vulnerable areas in any facility are the vehicle entry points. These pose a high risk for several reasons. The vehicle may be carrying an IED or other hazardous materials or may be hijacked and driven by a person with hostile intent, or it may even be driven into the facility with the known driver but under duress. In other cases it is there to be loaded with stolen goods without anybody noticing.The core function of any vehicle checkpoint is to ascertain the identity and integrity of vehicles and passengers passing through. This function may be repeated several hundred times a day with an almost identical process performed by security guards. Over time, the guards may get relaxed and as a result unconsciously lower their level of attentiveness to possible threats.
This fact is perhaps one of the most significant security breaches that a checkpoint suffers from. This is why technology aimed at addressing this particular vulnerability is essential.
Cornerstone can help you develop a simple and robust
vehicle checkpoint system
that automates the process of checking the identity and integrity of vehicles along with any drivers associated with these vehicles.Automatic Number Plate Recognition
In some cases, license plate recognition(ANPR)
is a useful tool to allow vehicle access but how do you know the vehicle is safe and just as importantly, who is driving it?This is where new technology is required to make sure both the vehicle and drive are correctly identified. Some questions that need to be considered are;
- Is the vehicle entering the facility carrying anything suspicious underneath?
- Is the vehicle entering the facility carrying anything suspicious or hazardous in the boot space?
- Is the regular driver driving the vehicle?
- Are there unauthorised passengers in the vehicle?

Under Vehicle Inspection
Vehicle checkpoint technology works by enrolling vehicles into a database by taking an image of the underneath and matching it to the license plate. When the known vehicle drives over the scanner it firstly checks if it is the correct number plate and then compares the real time view of the under carriage with the known image in the database.If the comparison checks out, the vehicle may proceed to the "driver" identification & verification portal where two factor authentication is required. If there is an abnormality or foreign material (see in the above image the software has identified an unusual piece of material in the red square) and displayed "Abnormality Found" on the operators PC, the vehicle can be subjected to further inspection.
However, if it is cleared by the operator the vehicle may to proceed through to the facility and a full audit trail is kept of both the vehicle and the driver.
Cornerstone Security Consulting has had extensive experience in harnessing the latest technology into workable designs to mitigate against the risks of hostile vehicles and manage vehicle access control and if you would like more information or like to discuss the various risks at your facility, please call us on 1300 952 785.
