Close the Vulnerability Gap and Reduce Administration Time by Linking Physical Access to Active Directory.
Using a common database for physical access and corporate infrastructure ensures extra tight security and reduces operating costs.
Security Issues with Former Employees
Imagine a company or organisation with many locations such as offices, warehouses, training centres and laboratories, etc. If a person is dismissed the HR team must send out paperwork and emails to all security managers in those locations who in turn need to invalidate that person’s credentials as soon as possible.If someone is dismissed Friday afternoon at 17:30 (or over the weekend) the first people to usually know are the human resources team and they instruct the IT department to restrict that person’s
access to the network
and IT resources. However, in some cases it can take a few days to remove them from theaccess control system,
particularly if their credentials must be invalidated by a security administrator or remote operator.We have seen many examples of persons being dismissed and still retain physical access to a building or site over the weekend where they can wreak havoc before they are fully transitioned out of the system. This is very common with organisations that have multiple sites spread across the country.
Furthermore, what if there is a large merger or acquisition and the cardholder databases for the new locations are different in format and structure? This scenario leads to a complex and lengthy task of re-enrolling the new cardholders into the original system. This transition time can also expose the company to
security vulnerabilities.
Is the risk worth it? The answer is usually no and that is why we recommend engaging asecurity consultant
to advise and guide your business to implementing this important solution.Increase Security and Centralise Administration
In terms of increasing security andcentralising credential management,
it is vital that any medium to large organisation links the access control system to their active directory or human resources database. Linking the physical access system to corporate databases used to be very convoluted and required the skills of software engineers and heavy commitment from both IT personnel and vendors.However, things have changed dramatically and the software to enable this important interface is now usually bundled into the core product of most access control manufacturers. It may require a software license, but its available "off the shelf" and easy to install.
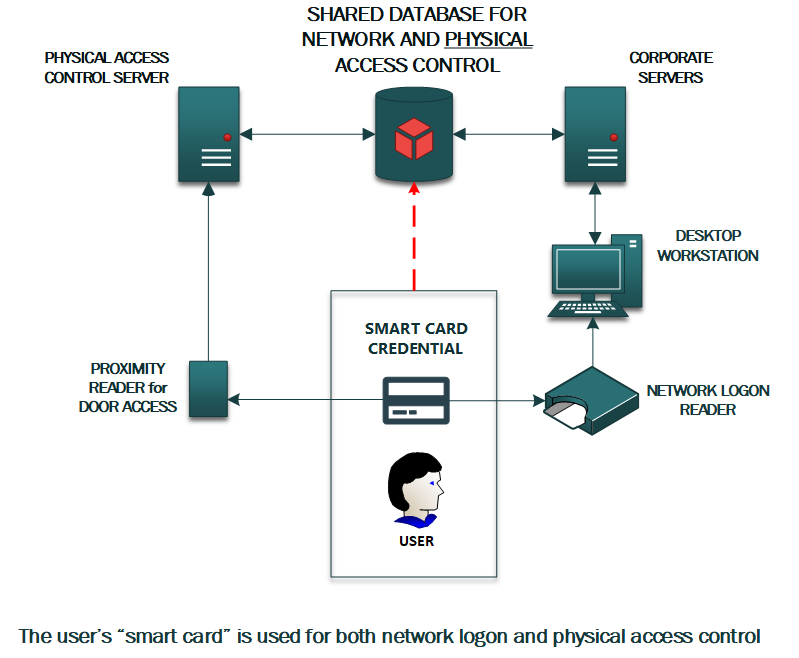
One Database Links Two Systems
As a result of linking the two systems, the configuration now relies on one secure database that is referenced by both IT infrastructure and physical access control systems. Usually this is Microsoft Active Directory but can be any database used by the organisation that permits "read only" queries. This basically means that any addition, modification or deletion of an employee’s status and privileges is immediately updated from the active directory database to the physical security systems, wherever they are located.So, if you had multiple sites, and they were linked to head office active directory, any changes are sent to remote systems without human intervention or errors. Additionally, new employees that have access to multiple sites only need to be enrolled once. This results in a significant increase in security and reduces administration costs.
Prevent Absent Logons
The above configuration also prevents people logging onto IT resources if they are not actually in the building (i.e., unauthorized working from home or giving their network logon card to another person). Basically, if the access control system has not registered the person on site, the IT infrastructure will refuse to let them logon and thus issue an alert to the security department. By extension, the convergence of the two systems enables single sign on, thus reducing the number of cards that people have to carry with them.These initiatives, along with many other time and cost saving schemes can be developed to help your organisation maintain good security and realize significant cost savings.
